- JTEKT TOP
- Sustainability
- Governance
- Risk management
Risk Management
Basic concept
Enhancing corporate value and meeting the expectations of society
We aim to continuously improve our corporate value by controlling risks ,uncertain factors in achieving our businness plan across the entire group, within expectations through integrated risk management.
We are working on risk management for the entire company based on the following items as a basic approach in accordance with the "Risk Management Rules" that apply to JTEKT and it's group subsidiaries.
1. Preventing and reducing risks that have a significant impact on management
2. Establishing a system to minimize damage in case of crisis
Promotion structure
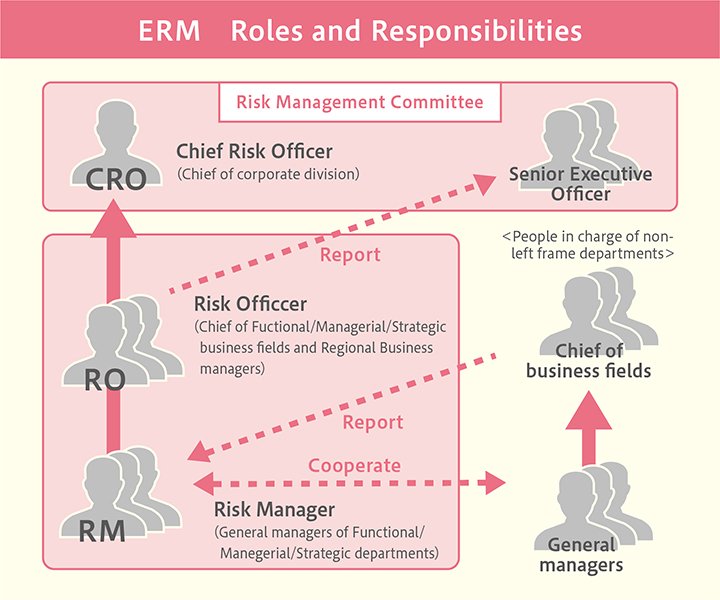
We have established a risk management committee chaired by the CRO (Chief Risk Officer), who is responsible for risk management. We have established a system to effectively and regularly update risk assessments and responses that incorporate external/internal environmental changes and are implementing follow-up measures to ensure that they are firmly established.
In addition, when a crisis occurs, we establish a crisis management headquarters according to the degree of impact and respond to the crisis.
Clarification of risk appraisals and response
At JTEKT, we conduct risk assessment activities for each business axis, functional axis and regional axis. Every year, we use the "risk register" created by major organizations in our company and domestic and overseas group companies to evaluate the impact and likelihood of risks that may hinder the achievement of our organizational business objectives.
The risks that have been determined to require priority response is being promoted across groups by the risk management department in charge of the risks.
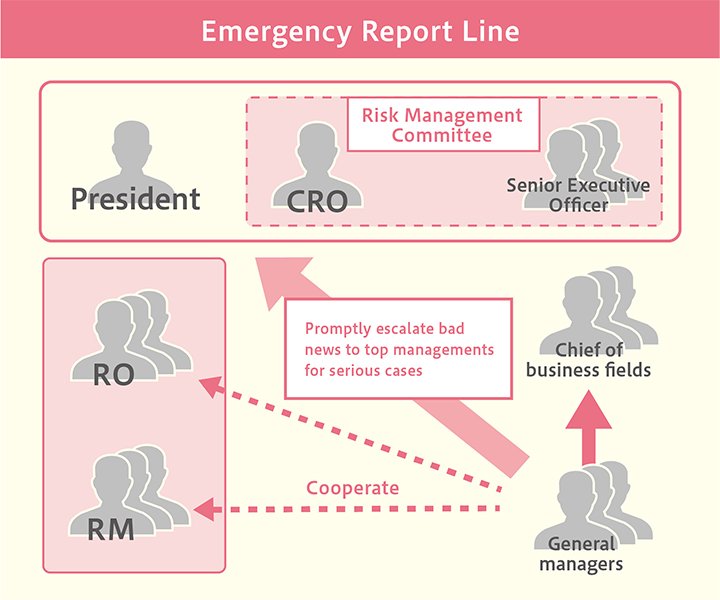
Enforcement of immediate reporting
We have expanded the scope of immediate reporting that requires prompt reporting after identifying compliance issues since 2015. We are also working on thorough enforcement of operational rules and establishment of a system to ensure that the first report after identification of other risks is promptly communicated.
Promotion of each division's risk activities
Internal penetration and enlightenment activities
There are various risks such as quality fraud, labor accidents, climate change, natural disasters, and information security. To increase sensitivity to these risks and to ensure appropriate responses are taken, various enlightenment activities are being implemented to promote understanding of risks and raise awareness. The main initiatives for 2023 include risk management training for executives (Strengthening the ability to foresee risks - Creating a corporate culture where opinions and true feelings can be freely expressed) and training for risk managers (risk extraction, risk scenario workshop)
Information Security
We recognize that information security risks, including cyber-attacks, are increasing day by day as a critical management risk, in order to supply secure products in each process of product development, manufacturing, and shipping, in 2019, we established the "JTEKT Group Policy of Information Security".
We also established a CISO (Chief Information Security Officer) and a department specializing in security in our organization in 2022, JTEKT is continuously working to strengthen measures against security threats to our products, the JTEKT Group, and related business partners.
Countermeasures for a Large-scale Disaster
Amongst the various risk responses JTEKT promotes, in regards to large-scale disasters with particularly heavy impact on continuity of business activities. In accordance with the Basic Policy for JTEKT Group BCP * formulated JTEKT is promoting countermeasures for both tangible and intangible aspects, such as confirming safety of employees, emergency training, measures to mitigate disaster-related damage in households assuming various regional disaster risks and preparation for the early restoration of product supply.
* BCP BCP is an abbreviation of Business Continuity Plan